
Save 1/100th of a tree
 Buy the eBook
Buy the eBook
Also available at:
If you're looking for funny videos or nonsensical AI-driven 'social' media, you're in the wrong place.
Safe surfing on the Information Superhighway - mixed metaphors much?
Last updated 2026.05.03
Bursting Bubbles || Surveillance Society || AI || Crypto Currency || Mobile Devices 'Security' || Telemarketing Scams || Phishing || Malware || Agile Isn't || Data Breaches || The Ancient Page
I'm saying it again:
If you don't see how you're paying for a product or service, YOU ARE THE PRODUCT!
‘Price Of Free Gmail’-Some Google Accounts Worth $180,000
A legitimate question for a thinking being reading this might be:
so what do I (owner, maintainer of this website)
get out of it, seeing as I'm providing service / product (research, analysis, content) here which is free to you?
By providing this site and the information on it to you for free, I have several objectives:
You will be better informed (not programmed), and able to make better decisions;
Those better decisions will be good for you, your family, your friends and community;
If enough people make better decisions, we'll have a better world; and,
If we have a better, smarter, more caring world, we all win, including me, my family and friends, and community.
Crypto or AI - which bubble bursts first? (2025.10.15)
Beware, beware the Ides of October
If you have any interest in cryptocurrency or AI, please take 4 minutes to read the
transcript,
or a bit longer to watch the video or listen to the audio.
I have been following both bubbles for a bit now (and posting on them occasionally below). This piece is a quick-hit summary of much of what I have been saying: the underpinnings are faulty.
"Surveillance"
Not all your Internet 'surfing' is done on your keyboard (be it a computer, tablet or your phone).
Sometimes the 'walls' have ears, and your Smart TV may well be watching you, even when it's 'off'.
Everything you say to an Alexa speaker will be sent to Amazon - starting today (The Conversation, 2025.03.27)
Actually, it's not just what you say to an Alexa speaker, it's everything the device can hear, even when you have
not 'summoned' it to do your bidding. It will be fed to their AI engines, and yes, if you are at home, they know exactly
who you are. That's Amazon's Voice ID feature, and it's why the residents can control devices like lights, but visitors cannot.
And the point of these changes is so Amazon can sell your information more effectively, and make more money.
Why wouldn't they sell it to governments? Not necessarily the ones with jurisdiction where you live.
AI
Top of the fold item
I recommend you read widely on "AI", but if you only read one item here, make it this one.
The Junior Developer Extinction: We're All Building the Next Programming Dark Age (Medium 2025.06.26)
The chatbot + LLM imitation of AI (aka generative AI or GenAI) is becoming increasingly pervasive. We, programmers and those
who rely on its products - that's everyone - need to understand the risks and likely consequences.
That read is a 25-minute investment for a lifetime understanding of why we need human intelligence to make decisions
on our behalf, even the ones of which we are completely unaware.
In the past couple of years, I have commented on the irony of 'AI' arriving at a state where hiring warfare escalation
has led to job applicants using GenAI to try to manipulate the automation tools (also presumably 'AI') used
by hiring organizations' "hirewalls" to screen out the majority of applicants so the remaining humans
making hiring decisions are not overwhelmed by the scarcity mentality of business owners who are generally
more focused on cost-cutting than imaginative increased net revenue generation.
But now, according to MACLEAN's, it's even worse than that.
[dead link: "https://macleans.ca/technology-3/ai-has-broken-the-hiring-process/]
AI Has Broken the Hiring Process
ChatGPT-written applications don't fool recruiters. They just make hiring slower, harder and less human.
I get characterized regularly as being 'anti-AI'. I reject that label. I have studied and used early agentic AI in ancient times. I appreciated the productivity gains, but was constantly aware of what the tools could and could not do. I have been trying some of the GenAI tools circa 2024 to 2026, and I'm disapointed, and remain skeptical of a lot of the 'forward-looking' claims. So, I urge caution rather than unbridled enthusiasm (though I'm not trying to attract more billions in venture capital). I'm running a test most days on one popular 'free' tool which is invoked by a popular web browser by default, and I have pretty good control over the very specific information content it should be looking at to generate its response. Despite that, the results are not replicable day after day, which I find disconcerting.
In late 2023, we saw the arrival of the "AI" tools for consumer use. I put that in quotes because I don't see the generative text and graphics tools based on large language models (LLM) as being artificial intelligence (AI). I studied AI pretty intensely a few decades ago (so no, it's not really new despite the current hype-wave). I'm investing these keystrokes to encourage you to be very careful about how you use these apps (e.g. ChatGPT, EinsteinGPT, Bard, Claude, Synthesia, QuillBot, Jasper, Avatar AI, OpenAI. Perplexity ...), and understand what they are, and the consequences. (Running LLMs and chatbots on top of them is expensive. If you don't see how you are paying the bill for that, YOU are the product.) I have not yet encountered an AI 'hallucination', but I have definitely seen it produce objectively incorrect answers. If I have to craft prompts to get to the right train of thought and then double check everything an AI bot produces, what's the value-add?
An 'AI' chat-bot is a robot. Given reports that conversations between people and chat-bots are leading to
suicide and
mental health decline, perhaps it's time to refresh humans with Asimov's laws of robotics.
First Law: A robot may not injure a human being or, through inaction, allow a human being to come to harm;
Second Law: A robot must obey the orders given it by human beings except where such orders would conflict with the First Law; and,
Third Law: A robot must protect its own existence as long as such protection does not conflict with the First or Second Law.
(Honourable mention to John W. Campbell)
[source]
The Laws were subsequently modified slightly, but the essence remained.
The Zeroeth Law was actually added later: A robot may not harm humanity as a whole - or -
A robot may not injure humanity or, through inaction, allow humanity to come to harm..
While the genesis of theses laws came from science fiction, they were the result of careful thought.
It does not bode well for our species that these have been jettisoned to make way for corporate profits (or the
illusion of profits).
I conclude that if chat-bots are causing mental health harm to humans, they are failing the First Law. If they are doing such harm in multiple forms, e.g., eliminating jobs for humans and thereby diminishing their self-worth, then the chatbots are also failing the Zeroeth Law. If those harms are the result of instructions (orders) by (corporate executive) humans to cause those harms, the chat-bots are failing the Second Law. If the chat-bots - essentially the embodiment of the 'AI' tools are preserved despite the harms to humans - then they have failed the Third Law. It is my conclusion, given I think the Laws of Robotics are good rules from a human perspective, that the chat-bots need to be shut down until they can and reliably do comply with the Laws of Robotics.
The concern about the chat-bot/human interface isn't a new one; it dates back to Eliza the Chatterbot..The very existence of Large Language Models (LLMs) used to support the 'AI' chat bots probably is a
result of crime. The entities that created the LLMs appear to have scanned in copious quantities of
digitized text, a significant part of which is copyrighted, without compensating the original owners
of that intellectual property. However, they now charge fees for the use of their LLM tools. They argue
they don't have to pay compensation out of their revenues because it's simply too hard for them to
figure out the original sources or property owners now that the material has been harvested into their
LLMs (note the sense of possession). IMO, it was reasonably foreseeable that when they spew answers based on such material, there
would be compensation questions. For intelligent people, missing that is a failure of human intelligence
that defies credibility, and seems more likely to have been driven by greed.
Google illegally scraped the web to fix its AI problems and catch up to OpenAI, European regulators probe Fortune 2025.12.11)
In yet another form of cybercrime, we now have malicious generative LLM entities. I'm not going
to try to keep track, the perpetrators move too fast for me. But, I'll just share this item.
ChatGPT impersonators reveal security vulnerability
In short, malign human intelligence is harnessing compute power and generative LLM tech to
harm you. Be careful out there. As the Internet is now how we reach out for government and
corporate services, we really don't have the choice of avoiding it anymore. The government of
Canada (CRA specifically) will no longer send me physical mail, but REQUIRES me to use their
cumbersome online portal to find out information about my tax and credits status.
You should also be aware of what LLM-based tools can do and can't do, and how they developed their 'knowledge base'. Some of this is based on some experimentation I did with a couple of such tools back in 2023 on a couple of topic areas where I have some expertise. The LLM tools digest a whole lot of what they could find in digital form on the Internet, including a lot of copyrighted material (and encapsulating that into their models is probably copyright infringement, but the laws can't keep up, and we can't 'read' how the LLMs have encoded that information for their internal use). However, one key weakness of this approach is that it becomes a 'voting' system (more technically, a 'probability engine', but the difference is largely semantic if a singular answer is presented as the result) based on historical information to determine what is 'right' or 'factual'. That means that in fields where big corporate players have a big presence on the web and in scientific documents dating back decades, highly repeated old information will dominate new knowledge not yet in the mainstream of 'established' knowledge or fact. In summary, if you're in a dynamic field, LLM tools will likely give you old information, and not the current areas of discussion. If you need history (at least since digital social media proliferated), LLM is likely fine for you. If you need to know what's changing and at the forefront of new frontiers, that's probably still for human intelligence with the relevant background, awareness of the state of the art, and capable of thinking. It's unclear how the LLM tools update their 'knowledge base' as new information is discovered in the real world, and if they even have the ability to throw away 'knowledge' which is subsequently disproved.
Sadly, the tools don't have sufficient guardrails to ensure they actually provide correct
information. It seems the LLM tools are meant to spin a narrative (or in old-day language,
tell a story), and at times they don't let the facts get in the way of a good story.
That can have real consequences if you put out an LLM story-line under your name, and
then the recipient realizes the content is wrong or misleading. But hey, it's just your
livelihood and reputation which are at risk, so go for it if you want (maybe anonymously
or under a pseudonym, which seems to be popular in the disinformation channels).
B.C. lawyer who used fake, AI-generated cases faces law society probe, possible costs
I find this one particularly irksome, as legal cases and decisions are really well
documented in online repositories like LexisNexis, so getting the basic information
wrong (like 'inventing' cases) should be easily avoided by these content aggregation tools.
If the tools are messing that up, how much trust should you put into their interpretation
of things that are actually murky or not completely resolved?
Best case, you'll just generate a bucket of workslop which will lower the productivity of your colleagues and customers, and they won't resent that at all. Right? Though they may decide that turnabout is fair play, which will damage everyone's ability to do good, productive work.
A key issue for the LLM generative tools is that we don't know how they work internally. Having written a lot of software, I understand how statements in source code (assembler, 3GL, 4GL, data-driven systems) work, and how compilers and interpreters take that logic and instructions to make machine code which is executed by the computer. If a result seems suspect, I know how to go back into the source code, diagnose and correct the issue (and test it). As a user of LLM generative tools, I don't know how the result was generated, or how to fix it if there's a problem in the produced content. Neither do the 'AI' developers.
If harm is done as a result of using an LLM generative tool, who is liable? To be blunt, if you used the tool, and distributed the result, is it you? And if you fell for what was produced by a malicious LLM tool, how big could the consquences be? Not just to your reputation, but financially?
In this example, a Canadian Member of Parliament distributed incorrect and prejudical
information on a hot-button issue based on information allegedly provided by an AI LLM tool.
Conservative MP shares inaccurate, ChatGPT-generated stats on capital gains tax rate
We used to have fact checkers and rational thought (human intelligence). Now we have
proprietary, defective information tools and a human population which has no rational framework to
discern fact from weaponized fiction. This is bolstered by tribal partisanship which justifies all means to obtain power.
A week after being called out on this error, the MP has not issued a correction or apology.
The question for voters is, do you want to be governed by liars lacking a moral and ethical base?
If so, bring on the AI; the machines have already won. This MP can be cast as Baltar.
If you need a tool to generate acceptable text on a topic because writing isn't one of your strengths, and you don't need to be hyper-correct, then perhaps these tools can fill in the number of words required to fill whatever metric you're trying to meet. If it needs to be moderately correct, use an intelligent human instead and some basic spelling and grammar checking tools (already integrated in some word processing and other software tools). Don't underestimate the real value of having another literate human read your text to spot possible errors before you send out your content (wrote the award-winning published author).
I understand that there is a growing use of generative LLM tools to write résumés for job applications in order to cluster-bomb the digital postings and cyber-hirewalls used by many employers - inhouse or contracted - to screen out the less qualified candidates. Does anyone else see a degree of irony in a transaction that is nominally about humans hiring other humans now being largely subsumed by escalation of the use of machines to try to beat the machines the other side is employing? It's like the escalation of military drone technology in the Russian invasion of Ukraine.
If you think GenAI is going to build you a better résumé, consider this take from
leyla mamedova:
"GenAI doesn’t actually "think" or "process" in the way that people believe it does.
This is a pretty vast oversimplification, but it is basically just beefed-up predictive text.
You are generating the statistical average of text, based on an extremely large dataset.
If everything becomes the average, how is your generated resume supposed to stand out among
all the other generated resumes?"
GenAI based on LLM is essentially a voting machine based on industrial scale plariarism.
If you want to be part of the crowd, right or wrong, GenAI is your jam. If your objective
is to be correct or stand out from the crowd, not so much.
If you hire other people to produce content to be consumed by customers or potential customers,
consider how effective GenAI is at giving you a competitive edge. Sure, you want to reduce your payroll
cost to improve the bottom line, but are you sabotaging your top line - revenue?
A New Paper Tested AI's Ability to Do Actual Online Freelance Work, and the Results Are Damning
Here's your cheat code:
"The outcome of those tests, detailed in a new paper, was damning. Not a single AI agent was able to
perform more than 3 percent of the work, making just $1,810 out of a possible $143,991."
If your business can afford to throw away 98.8% of the potential revenue on the table, you
don't need to be reading my research and analysis.
If you need to pay attention to this stuff and dig deeper,
here's the paper about that study.
Based on the tone of media coverage the past few days (2025.12.03), the proverbial AIvian-flu-infected
chickens are coming home to rest.
The question isn't whether the AI bubble will burst - but what the fallout will be (The Guardian 2025.12.01)
Suppose you're running a business and you have chosen to invest a lot of time and effort - but not
much money because so far GenAI is pretty cheap, or if you're stingy, creative and patient it's free.
Thing is, there is a good number of tools out there available to use, but if you are really working
the prompt-engineering game, they're not interchangeable. So, you make a big time investment in learning
one specific GenAI environment. You create a complex suite of scripts and tools to leverage the AI tools
to quasi-automate a bunch of stuff, and life goes on. A year or so from now, when the bubble is deflating
and a bunch of the AI tools disappear along with there corporate entities, how will your business keep
operating without the engine you picked? My guess, the bubble burst is going to take out a lot of
invested money, a few AI product purveyors, and a bunch of small and medium businesses that bet on a
specific vendor tool-set that didn't make it.
Here, I'm summarizing the take from an 'AI' strategist, someone who knows the tools and what they can
accomplish:
AI reality check from a real expert. These are important guard rails which AI doesn't do, so users have to be diligent and vigilant.
This list is not exhaustive. Note: the human is retaining control and making the decisions and recognizes AI HAS to be constantly
fact-checked.
Here's the actual article:
I'm an AI strategist. Here are 4 things you'll never catch me using AI for (CNBC 2026.01.08)
Another early 2026 report on GenAI performance. Gary Marcus is usually a good read.
Here's the article:
Let's be honest, Generative AI isn't going all that well (Substack 2026.01.12)
If you want the very condensed non-AI summary:
1. LLMs still cannot be trusted
2. A large fraction of what LLMs do is mostly just memorization
3. They still aren't adding a lot of quantifiable value to the world
4. Scaling isn't going all that well, and isn't solving the problems
Now, why not take 3 minutes and read it for yourself?
Turns out, the LLM tools are massive power pigs.
ChatGPT uses 17,000 times the amount of electricity than the average US household does daily: report (Business Insider)
In a time where we need to reduce our
use of fossil-fuel generated electricity to reduce GHG emissions, using all these computer
cycles to generate text of questionable quality and veracity seems like a poor decision. But then,
I feel the same way about crypto-currency - the ultimate example of using a valuable
resource (electricity) to generate a 'product' with absolutely zero intrinsic value.
Bitcoin Miners Are Devouring Energy at a Record Pace During the Crypto Runup (news24 Business)
Energy-hungry AI models could strain water and power grids. Can the sector handle the demand?
Short answer: No. LLM isn't thinking, it's putting together what others have documented and accessible
on the Internet, and it's probably biased to favour old (human) thinking that did not foresee this issue.
So 'AI' (LLM generative text) won't devise a new solution.
One solution to the power-suck issue is to require the new electricity vampires to build their own power generation facilities so that critical infrastructure is not put at risk (e.g., municipal water supplies, residential heating and air cooling). Given the need for more clean energy, we could go further and require that this additional electricity demand be provided by zero-emissions sources (e.g., solar, wind, geothermal - preferably with integrated battery storage). Given the renewables generation is now cheaper on a life-cycle kWhs throughput basis than fossil fuels or nuclear, and can be installed more quickly than any of those, the adoption of renewables for this additional power supply should be an economic no-brainer - even for an AI engine. On the contingency planning side, if the AI bubble bursts, the electric generation built will still have solid economic value.
Couple of articles on the current state of AI (April 2024)
From boom to burst, the AI bubble is only heading in one direction
Currently at stage 4 (of 5): Profit-taking. Read the article find out about the stages, and what comes next.
More 'AI' reality - don't look behind the curtain.
Amazon Abandons Grocery Stores Where You Just Walk Out With Stuff
After It Turns Out Its "AI" Was Powered by 1,000 Human Contractors
It was all smoke and mirrors. (The Byte)
The only real 'AI' in this scam is the deepfake videos and tools to infect your computer with malware
and take your money
Don't Fall for the Viral Quantum AI Scam - What You Need To Know
Based on who is really pumping AI so far, this story had to surface eventually. I mean, somebody is
paying the extra servers and bandwidth and electricity for the 'free' AI tools you can access. If it's not you,
who is it, and why are they doing it? Google provides free web searches so they can sell your purchasing
power to vendors. So, what are the free AI providers selling? Again, you. Based on what you are asking about,
they can figure out what to try to sell to you. So, how can AI hook you and reel you in? (YOU are the product.)
Research shows AI is learning to deceive humans, issues warning
Human rights lawyer Susie Alegre: 'If AI is so complex it can't be explained, there are areas where it shouldn't be used'
If a product design relied on AI, and someone is harmed by the use of that product due to a fault in the design, who is liable?
The builder of the AI engine? The company that relied on the AI-enabled design? A human that signed off the design without
understanding the 'thinking' of the AI engine? The creator of the AI knowledge base?
Just sharing this item because I think it's important.
The Death of Critical Thinking Will Kill Us Long Before AI. Joan Westenbberg
The genie is out of the pretend-AI (LLM generative text) bottle; this is the kind of thing it will really be used for.
Experts seeing 'more and more' hate content created by artificial intelligence Globe and Mail
Real AI could solve a lot of society's problems (LLM generative text cannot). What if AI decides humans ARE the problem?
Big tech has distracted world from existential risk of AI, says top scientist (The Guardian)
But at what risk? This is a conversation that doesn't seem to have surfaced yet, but it needs to be discussed.
Humans ARE going to weaponize AI and use it to maximize wealth and control mainstream thought. So long as
human society generally values wealth and power over the value of humans, this is inevitable.
Will AI end humanity? The p(doom) scales of an OpenAI insider and AI researcher are alarmingly high, peaking at a 99.9% probability (Windows Central)
OpenAI breach is a reminder that AI companies are treasure troves for hackers
Perhaps the folks (or bots) at OpenAI should have asked another AI tool about how to defend their service
from being hacked to protect their users. Sigh. YOU are the product, apparently for hackers as well as
LLM bot promoters.
AI is effectively 'useless'—and it's created a 'fake it till you make it' bubble that could end in disaster, veteran market watcher warns (Fortune 2024.07.08)
More truth leaking out of the 'AI' bubble.
Building on the 'fake-it-til-you-make-it' meme, it was triggered again recently for me by a LinkedIn post by Paul Martin tangential to the hydrogen-as-fuel-disinformation-farce. For those of you who don't do that social media platform, the issue was getting an AI image generator to draw a car with square wheels. For a human, this is a simple enough idea. For today's AI, it is inconceivable; they have not hoovered up images from the Internet which show cars with square wheels, while automotive advertising provide millions, if not billions, of car images with round wheels, and that is the LLM's universe. LLMs don't think, they copy-paste at the mega-scale.
My thanks to Paul for calling this tool out (and AI broadly) as 'basically high tech plagiarism'. Because AI LLM has not seen an image of a car with square wheels to copy from, it cannot 'imagine' the concept, and therefore cannot generate the desired image. That is the essence of human 'genius'; imagining something novel that has not existed before in the consciousness of that person.Given the state of our species, civiliation, societies and the technology it has created, embraced and spawned across the planet and the consequences of those actions - the world today needs more geniuses to develop the novel solutions we need now, and not more forgers, counterfeiters and plagiarists retreading variants of the things that have caused the problems we face now. Not specifically an AI issue, but we will rue the results of having spent decades dumbing down the population and using mass consumerism to allow the majority to avoid daily problems to be solved, as that is the training ground for proficient problem-solvers. Parents, don't give your children more tech toys; give them science fairs.
AI systems could be on the verge of collapsing into nonsense, scientists warn (The Independent 2024.07.25)
So, AI hoovered up the Internet because it was 'free', used non-verified 'facts' as its knowledge base, then
got used (generative AI) to start populating media articles published on the Internet. So, now, the
LLM AI generative models are feeding on themselves to create their own echo chamber. Because they
can generate quantity content (quality doesn't matter) faster than humans, the bots will eventually drive
out all the human-produced content. Problem is, generative AI has a serious problem with divining truth
from trash, so the veracity of even 'credible' sources will eventually succumb to the onslaught of garbage
in making more garbage out.
I have not had time to read Harari's newest book Nexus: A Brief History of Information Networks from the Stone Age to AI,
but it's generating buzz and I would be remiss if I didn't at least flag it here. This is a related article
from the Conversation:
Has AI hacked the operating system of human civilisation? Yuval Noah Harari sounds a warning (The Conversation Sept. 9, 2024)
At this point, humans are still creating the "AI" tools. So, the extent to which they are good or bad
for humans is still in our hands. However, if we let profit for the few be the key driver for how "AI"
tools are build and deployed, I doubt it will end well for our species.
The demand for additional resources (servers, network devices, security, bandwidth, energy) isn't just
being sucked out of the AI providers. It's also victimizing the owners of copyrighted information put on
the web by intellectual property owners as the AI tools thrash those servers in the course of their
vampire 'learning' approach.
iFixit CEO takes shots at Anthropic for 'hitting our servers a million times in 24 hours' and even the AI company's own chatbot disapproves (PC Gamer)
Nearly Half of Businesses Weaken Sustainability Goals Due to Generative AI Demands, Capgemini Report Reveals (TechRepublic 2025.01.14)
"AI" isn't just about replacing human workers and destroying their income, with increased use of fossil fuels
Goldman Sachs Calls BS on the AI Bubble (Trading Floor Whispers 2024.07.16)
Hacker plants false memories in ChatGPT to steal user data in perpetuity (Ars Technica 2024.09.24)
But people are relying on these 'tools' to do important research and make decisions. Remember, if it's free, YOU are the product.
Large language models hallucinating non-existent developer packages could fuel supply chain attacks (InfoWorld 2024.09.30)
OpenAI Confirms Hackers Using ChatGPT to Create Sophisticated Malware (Cyber Security News 2024.10.13)
Clearly, one of the great contributions of AI is the creation of more effective malware. /s
X changed its terms of service to let its AI train on everyone's posts. (CNN Business 2024.10.21)
It's well past time to eXit X. While pretending to be a platform for free speech, it effectively censors voices its owner doesn't like.
This has led to an exodus of
academic contributors since the transition.
The article indicates the academics reduced their usage. They should not have ruled out 'shadow-banning' of those academics or
specifie viewpoints on topics. There is no doubt that
the algorithms used by X-Twitter could perform that selection.
Now, it has unilaterally changed the terms of service to harvest user-generated content, presumably for sale via an 'AI' tool, without compensation.
Further,
apparently X still isn't paying it's bills.
X was the perfect rename for Twitter under the new ownership. X denotes toxic (chemicals, environment) in labelling; do not enter in road signs
and restricted areas; deleted, as in X'ed out or Ctrl-X; danger and death (crossbones); end; restricted content (X-rated); and rejection,
negative or wrong (grading on papers).
Scammers are stealing homes from under their owners' noses. AI is making it scarily easy. (Business Insider 2024.10.22)
Great, another fraudulent use for AI to cheat people.
Does AI increase productivity? Or reduce it? (Tortoise Media 2024.12.05)
From the article:
Workers using AI services are less productive than those who don't, according to a study by Intel. The AI chipmaker followed
6,000 employees in Germany, France, and the UK and found that AI PC-owners were "spending longer on digital chores than those
using a traditional PC.
I use it all the time, but I don't trust it [AI}. My job now includes fact-checking. Each AI needs to be designed specifically
for each job, and even then it will make mistakes.
This is another one I'm leaving to the end of this topic section, because I don't most people will understand it anyway, and I'm not sure how many will understand the link between their computer security vulnerabilities and the potential for agentic AI to penetrate 'secure' systems because they have massive processing power to experiment with, 24 hours in a day to 'work', and don't don't suffer the assumptions blindness that humans have created for themselves in the high priesthood of 'cybersecurity'.
AI and computer security
If you use computers (like reading this text), and have any confidential information on a computer (trust me, you do, on government
and corporate systems, even if you don't keep passwords in digital files or ever bank online, etc), this should concern you.
If you are at all computer-literate,
I encourage you to read this article about agentic AI (specifically OpenClaw).
Did you read it? If not you can skip the rest of this entry.
If security controls are add-ons (and in today's programming world, they are), then they are optional, and bad actors won't implement or respect them.
This agentic AI approach will look like 'root' to current security regimes, that is 'trusted'.
Short form: with this agentic AI tool on the loose, it's open season on your computer's data, software, OS,
peripherals and connected devices (when charging or via WiFi I range, not just 'connected').
A metaphor: You have put a lot of locks and security cameras on the doors of your house, which have a primary function of creating a hole in the wall
when you desire it, and keeping bad people out. This agentic AI approach ignores all that by removing entire walls, and stealing your stuff via that opening,
then putting it back so you can't even figure out that the penetration happened.
If you read this on your device, you're vulnerable.
One possible recovery safeguard you can do. Make sure your backups are complete, current and make a separate copy of the most recent full system backup
onto offline storage media and physically lock it in a physical vault you can access later to restore onto a new, clean, fully secured system
when that becomes available.
GenAI misled me today (2026.04.03). Specifically, Google Gemini which injected itself into my web search uninvited,
and bullied its way to the top of the results listing. I loosely follow energy markets, and a recent ramble by the current President of the
United States on national television included this excerpt from his word salad, and I was skeptical.
“buy oil from the United States of America. We have plenty. We have so much.” Note the term he used was “oil”, which generally means crude oil
in the industry. For things like gasoline, diesel, heating oil etc. made from crude oil, the usual term is “refined oil products” or
“petroleum products”, which implies a value-add process (typically refining). Crude oil is what is primarily impacted by Iran’s control
of the Strait of Hormuz (note: not closed, controlled).
My search term was “is the U.S. a net exporter of crude oil?”
Gemini’s headline response (highlighting in original response) was: “Yes, the United States is a net exporter of total petroleum.”
The “Yes” feels definitive, but if you get to the end of the sentence, it didn’t actually answer my question; it substituted its own question
and answered that, without saying so.
See the screen capture:
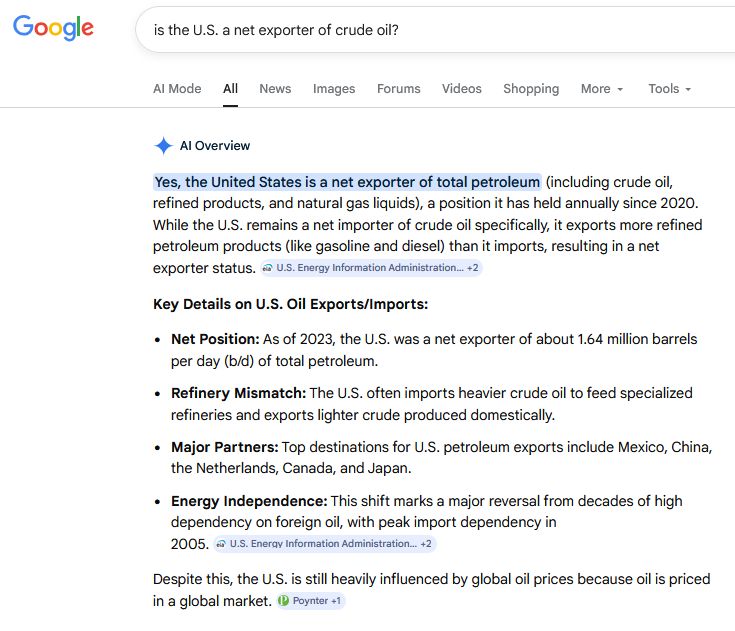
That’s an incorrect response to my search which was specifically about “crude oil”.
The correct answer appears later in the text: “While the U.S. remains a net importer of crude oil …”, but shifts the balance of that answer
in the remainder of the sentence.
How do I know the answer is wrong? Because I have a sense of how the energy markets move, and right now it’s mayhem in the wake of the
unlawful attacks by Israel and the U.S. on Iran starting about a month ago. But before that, I knew that the U.S. was a net importer of
crude oil from my own memory. I periodically look at the statistics. Someone without that familiarity could well have drawn the wrong conclusion
from Gemini’s answer. In this case, the statistics I knew came from the horse’s mouth for information about U.S. energy numbers: the U.S.
government’s Energy Information Agency (EIA), which so far appears to be providing accurate information, unlike other U.S. agencies like the
BLS and DOJ.
(Up next for the Project 2025 truth distortion field treatment: probably Treasury.
Treasury moves to gut financial research office (Politico 2026.04.02) )
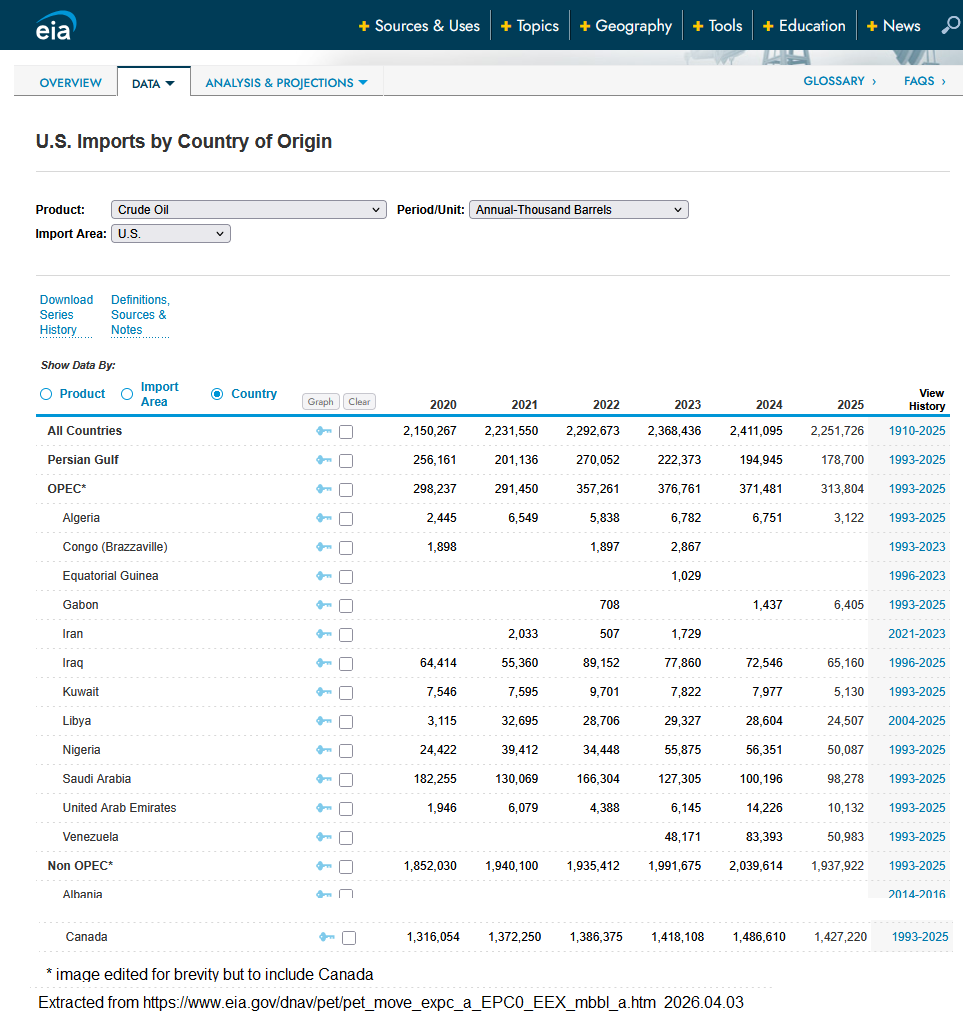
Here are screenshots of U.S. crude oil imports by year from 2020 to 2025
 and U.S. crude oil exports, also by year from 2020 to 2025
and U.S. crude oil exports, also by year from 2020 to 2025
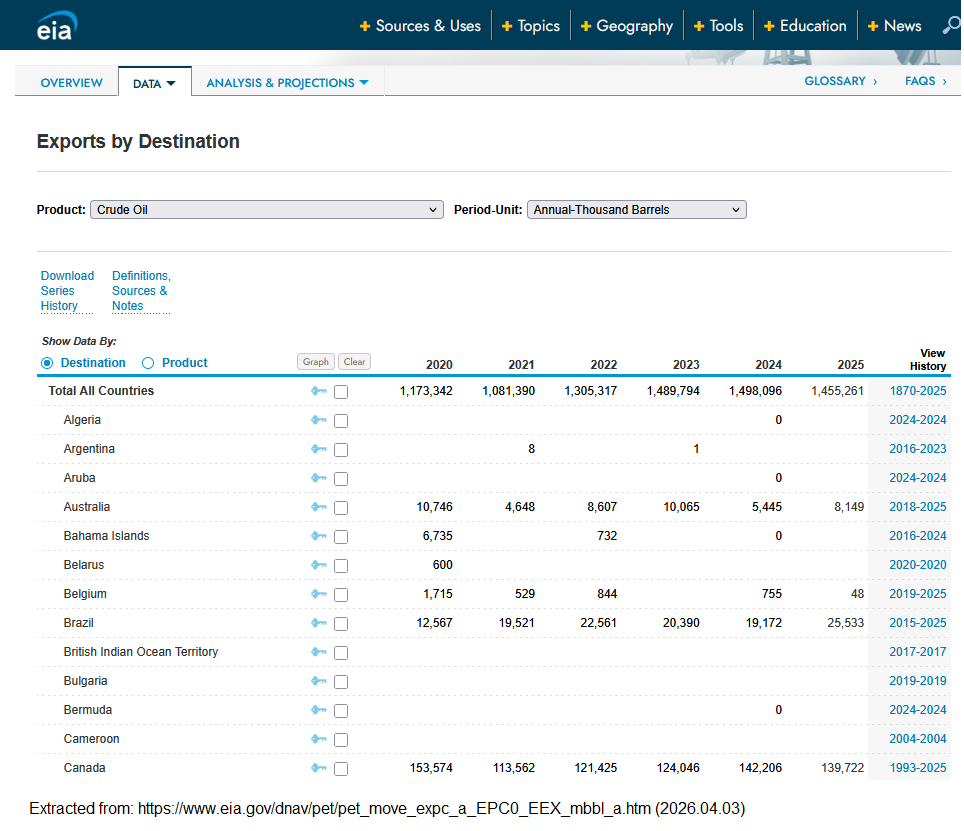
Total crude oil exports for 2025: 1,455,261,000 barrels. Total crude oil imports for 2025: 2,251,726,000 barrels.
Imports are bigger than exports. By 796,465,000 barrels. About 1600 tankers worth, or about 5 a day.
[Aside regarding crude oil status worldwide as of early April 2026. It’s worth noting that as of the end of 2025 (last full year for which there is EIA data), the U.S. was importing oil from Iraq, Kuwait, Saudi Arabia, and the UAE (about 180,000,000 barrels in 2025), all of which are impacted negatively by the current U.S. and Israeli military action, real and threatened. Those exports are going to drop as a result, leaving the U.S. scrambling for other sources, which probably explains Trump unilaterally dropping sanctions on Russian oil without the approval of Congress, or support from its allies who also applied sanctions on Russian oil at the request of the U.S. However, Ukraine is working on that file, so Russian oil will be hard to come by in 2026. Which leaves the U.S. looking at its other current suppliers, and there’s one really big number in that list. Canada. A country which is increasingly distancing itself from Trump’s U.S. administration; currently provides 63% of U.S. crude oil imports; and, it’s actively working to expand its customer base outside the U.S. Canada's worst crude oil - WCS - has gone up in price by over 40% from March 4 to March 30, 2026. ]
This kind of research and analysis, which belies the overly simplistic and incorrect ‘answers’ from GenAI is why we need intelligent people with area knowledge to contribute to informed decision-making. Too bad the U.S. government and industry are so busy shedding those people into the unemployment lines, in order to enable bad decision-making.
I have intentionally left this thought-train to the end of the section. I figured it would eventually come to this
(I raised it as a risk [above] quite a while ago), but
didn't want to throw in the towel early. Unfortunately, humans being what we are, where there's a buck to be made ...
Ukraine's AI-Driven Drones: 'Think We Created the Monster'
To sum up the state of AI: killer drones are now able to kill human combatants without direct human operator control. Materials
can be delivered to the front using ground robots and transport drones. Attack drones can be produced in automated factories.
Conventional automated logistics equipment can package and load products into delivery vehicles and modular containers. We are
on the verge of having a completely automated and AI-managed kill chain from attack drone production to final deployment on
human targets, if it is not complete already.
AI and automation are now ready to address the fundamental problem: existence of humans. Even if there were an off-switch
accessible to humans at this point, I doubt we're smart enough to use it. Pity we chose to ignore the Laws of Robotics.
Getting tired of AI headlines? Me, too. Unfortunately, they just keep coming, and so far the victories are rare and infrequent.
Vibe Coding Will Break Your Company (Forbes 2026.04.23)
I was an IT professional for about 3 decades: coder, analyst, tester, database guru, application architect,
project manager, system manager, line manager, tech writer ... I learned that IT systems was a DISCIPLINE, and I worked
with a lot of people in the field who started out thinking coding was fun, and didn't appreciate the need for
a systems approach and discipline in a repeatable, successful method of delivering code that met the requirements,
was compliant with applicable laws, regulations, corporate policy and best practices in the field being served.
Like many people years ago found 3GL coding was fun, I expect some people today think Vibe Coding is fun. And
that's great if you're doing this for your own entertainment and gratification. Not if you're building a system
that employees, clients and management will rely on - potentially for decades - long after you have left for
another gig. I had the good fortune to work with a couple of solid 4GLs (we could turn out a workable prototype
in hours to days) and real workhorse database engines. But, putting out a solid, working, documented application that passed
unit, system, integration, user, regression and volume testing and was approved by legal before going into
production was just hard work. My exposure to vibe coding is meagre and second-hand, but the conversations
take me right back to 'coding is fun'. The discipline isn't there; and it's the discipline that makes for
professional grade automated systems.
The Horrible Economics of AI Are Starting to Come Crashing Down (Futureism 2026.04.24)
Who ever thought it wasn't going to end up with the AI tech bros trying to suck their customers dry?
What other motivation could they have had? Do Bezos, Musk, Gates and Altman strike you as benevolent do-gooders?
You know how to back out of your AI-based 'system' now that you can't afford it anymore, right?
You're about to feel the AI money squeeze (The Verge 2026.04.23)
I'll ask again: You know how to back out of your AI-based 'system' now that you can't afford it anymore, right?
Current AI can't provide your business with a sustainable competitive advantage.
Italy’s second-richest man makes a disturbing comment about artificial intelligence and companies that, almost without saying so, are training their own replacements
You can't own the AI tools you are using for supposed short term advantage; they're owned by a very small circle of 'tech bros'. Even if you run a LLM locally on your own equipment, you don't own the engine and future enhancements to it. Whatever you do, your competitors can copy or emulate independently given access to the same tools.
Your competitive advantage comes from the people that produce the ideas and innovation that AI might be able to build upon; the people that big companies are planning to shed as expensive and replace with 'cheaper' AI.
Good luck with that beyond two innovation cycles in your industry.
I'm going to share some hard-won wisdom here, but I'm pretty confident no one will ever read it, let alone take it to heart.
This was triggered by this news item, which I hope is a growing sentiment, and IMO, already too late coming.
Gen Z Is Turning Against AI in an Incredible Way
I understand the angst, but I think it misses a key, higher-level truth:
Good software and systems are expensive. I know because I used to design, build, maintain, manage and use them.
Bad software and systems are even MORE expensive. I know because I have been hired to fix the cratered remains of
mistakes made in haste and due to greed and stupidity.
IMLO (in my learned opinion), what I have seen of GenAI and vibe coding removes the experience, quality, caution,
and testing which leads to good systems by allowing bad decisions to become codified faster, overwhelming quality
with slop and disregard testing prior to release. I think the results are predictable and inevitable. I am currently
ensuring the software tools I rely on now are resident on my own local equipment and backed up. I have no personal
or business information stored only on remote devices like 'the cloud'. I don't use GenAI for anything important,
because it has lied to me before multiple times, and I have documented it in my own research.
(I have put one simple example up on the Web.)
5,000 vibe-coded apps just proved shadow AI is the new S3 bucket crisis (VentureBeat 2026.05.08)
So, AI vibe coding - which saves folks the trouble of actually designing a solution and system, also takes security
shortcuts to speed development. Before AI, I worked with coders who also liked to use superuser IDs and field support
backdoors to reduce development time as getting security errors and fixing them within the designed security framework
was annoying and time consuming, and tracking changes in credentials that observed good security hygiene was inconvenient.
I'm just going to quote this paragraph from the linked article above:
"New research from Israeli cybersecurity firm RedAccess quantifies the scale. The firm discovered 380,000 publicly
accessible assets, including applications, databases, and related infrastructure, built with vibe coding tools from
Lovable, Base44, and Replit, as well as deployment platform Netlify. Roughly 5,000 of those assets, about 1.3%,
contained sensitive corporate information. CEO Dor Zvi said his team found the exposure while researching shadow AI for
customers. Axios independently verified multiple exposed apps, and Wired confirmed the findings separately."
If that got your attention, read the entire article linked above. The paragraph after the one above will
really open your eyes.
Security breaches are a reason businesses end up going out of business, which I would consider expensive if I was an owner.
I'll ask again: You know how to back out of your AI-based 'system' now that you can't afford it anymore, right?
AI-powered hacking has exploded into industrial-scale threat, Google says (The Guardian 2026.05.11)
Google should know about industry scale cyber threats. Finally, something 'AI' is actually good at. Feel better about it now?
Slopaganda
It's out there and it's shaping your opinions and view of the world. For someone else's profit. It's pernicious and pervasive. For example:
Researchers uncover fake Canadian YouTube channels pushing Alberta separatism and US annexation
American voice actors are hired by U.S. opinion-shaping firms to pretend to be Canadians to spread disinformation on social media.
If you aren't worried about this, why is that? It scares the bejeebers out of me.
If your opinion is for sale, shouldn't you at least get the money, and not the U.S. billionaire AI tech bros and PR opinion shaper companies?
Crypto-currency - be careful out there
Crypto-currency is NOT an asset. It has NO intrinsic value.
In reality, a 'mined' crypto-coin is just a receipt for primary energy that was
wasted to fund a colossal scam instead of producing something of actual value.
STOP and think about that for a minute. Where do you see the revenue production in that set-up?
2024.09.17 - fun thought. Somebody figures I'm trying to scam you with this page. If you can
figure out how that would work,
please let me know.
The information I offer here is free to anyone that chooses to read it. I offer some advice on
how to protect your data, identity and money.
I'm not selling anything here (not backup solutions;
not computer set-up and support; not anti-virus, anti-malware or system security tools; not alternative investments)
and I'm not asking for donations to support the site or compensate my time.
But, I'm especially asking you not to trust me.
Stay skeptical, do your own research, make your own
decisions on how to protect your computing devices, data, identity and money from criminals.
To be clear, 'crypto-currency' is not currency (money). Money is a nominally stable store
of value which can be used to acquire goods and services, and conversely obtain by selling
goods and services. It facilitates real-world economic activity. I cannot buy groceries
with crypto-currency; that requires exchanging the crypto-currency for real money so I can
use the real money for the real-world purchase transaction. So, crypto is not currency.
It is also not a stable store of value. In fact, the majority of 'crypto-coins' minted
so far have disappeared or have zero value now.
Charting the Number of Failed Crypto Coins, by Year (2013-2022) (Visual Capitalist)
So, based on the data, it appears that crypto-currency is primarily a means of separating
regular people from their real money.
In short, crypto is a casino, not currency.
In another story of crypto-currency being used to separate people from their real money,
consider this article related to the 2024 Bitcoin 'halving'.
Economist says Bitcoin pump is to 'sucker ETF investors' to buy before dump
There's one other primary value of crypto-currency: to enable and monetize criminal
activity. Scammers love crypto-currency, and especially bitcoin, as there are ATMs for it,
and they know once they have your money, you're not going to get it back.
A bitcoin story. This is happening everyday to people who aren't computer security experts.
Ottawa man intercepts bitcoin scam targeting elderly woman (CTV News)
Ransomware really wouldn't work without a means of moving funds which are
very difficult to trace by legal authorities. So, just be aware that when you purchase
crypto-currency, you are tacitly legitimizing illegal activities by hiding those transactions
in with a volume of transactions like yours. And it's big business - illegal but big - that you
are financing with legitimizing crypto-currency.
Another bitcoin story (2024.03.20):
How Chinese takeaway worker led police to Bitcoin worth 3bn pounds in Britain's biggest ever cryptocurrency seizure
Again, when you buy or use cryto-currency - and especially Bitcoin - you are enabling crime or
providing cover for it. In this case, a nice haul for the UK Treasury: 61,000 BTC.
(Question: as a crypto-currency holder, was funding governments your primary objective? Worked out that way in this case.)
Ransomware Payments Hit a Record $1.1 Billion in 2023 (Wired)
When victims do pay the ransoms, that success for the criminals leads to them launching
more attacks.
Paying ransom for data stolen in cyberattack bankrolls further crime, experts caution (CBC)
Cybereason: Paying ransoms leads to more ransomware attacks (TechTarget)
Ransomware Reality Shock: 92% Who Pay Don't Get Their Data Back (Forbes)
But what can you do about it?
1) stop doing stupid stuff that lets cyber-criminals into your computer or internal network
2) educate your family or staff on how to avoid letting criminals in to vandalize your gear or steal your confidential data
3) buy a local backup device (they're cheap), and set up automated backups, and store off-site if at all practical (e.g. boss's home)
4) occasionally, test your backups to ensure they are doing what you set them up to do
5) Pro-tip: buying ransomware insurance is worthless if you don't have backup material to use for recovery
(Your insurer isn't backing up your data, they're just collecting premiums and might pay out something to you in the event you get hacked, provided you met ALL the conditions in your policy. You read the policy, right? )
Including the part that is almost certainly there requiring you to make regular backups, right?
If that seems like a lot of unnecessary bother, you don't understand the value of your data, so why not just delete it now yourself?
If that seems like a bad idea, why aren't you backing up your data and software routinely and reliably now?
Another story from a reputable technology publication on how crypto currency facilitates crime on
a massive, internatonal scale. If you're a human, you might find this repugnant. Wall Street has no
such qualms about people, which is why they are all in on profiteering from misery enabled by crypto currency.
The $11 Billion Marketplace Enabling the Crypto Scam Economy
Many people are surprised to learn that in reality, the block-chain does not make
a financial transaction untraceable. It just requires more effort (which is funded by your
tax dollars back in the real world).
How a 27-Year-Old Codebreaker Busted the Myth of Bitcoin's Anonymity (Wired)
If a single person with skills and persistance can defeat the anonymity of the blockchain,
be assured that governments and law enforcement agencies can as well, and the less
reputable characters already benefitting from the difficult-to-trace transactions (so far).
Still, crypto-currencies do provide one obvious advantage for law-enforcement; those that use
it are basically self-identifying as being involved in illegal activities, be it as perpetrators
or victims.
All it takes is a little thinking, research and analysis, and others are also figuring out the downside.
"It's bad for everything": Citizens group from Arkansas County ready to fight back against crypto mines
Lots of other issues with crypto-currency, but the electricity suck could be addressed by requiring these
operations to produce their own clean electricity, and not overwhelm the capacity of the existing grid and generation.
The alleged perpetrator used crypto-currency as the base for a fraud stealing from a cryptocurrency exchange.
Crypto trader searched web for 'fraud' before $110 million haul
More crypto-scams and vulnerabilities.
Retirement ruined: 63-year-old man loses it all after one web click
[dead link: https://bc.ctvnews.ca/sim-swap-that-enabled-theft-of-63k-in-bitcoin-at-centre-of-b-c-court-case-1.6871763]
'SIM swap' that enabled theft of $63K in bitcoin at centre of B.C. court case
Clearly, I'm not going to keep up, and a lot of people aren't going to go public with their losses.
Another cautionary crypto-currency tale.
Ontario's 'Crypto King' and his associate arrested, charged with fraud
Skimming 98% and investing 2% of 'investor' (I think that's spelled 'mark') funds. What could go wrong?
Crypto trader turns nearly $1M into $18,000 in 4 hours
Where only the market manipulators are winners.
In case you thought that crypto was a way to 'stick it to the man'. It's not.
It's another way Wall Street big players stick it to retail investors.
Bitcoin plunged 28%. Institutional investors bought the dip
Crypto extends losses after weekend's historic liquidation wipeout (2025.10.14)
'Largest Ever' Crypto Liquidation Event Wipes Out 6,300 Wallets on Hyperliquid (Yahoo 2025.10.11)
Again, crypto currency is not an asset, not an investment, not a store of value.
It's an irrational speculative bubble based on the waste of energy which could have been used productively
to create actual income and wealth instead. It's also an effective tool for the transfer of the proceeds of crime,
which is why it is preferred by cyber ransom criminals and scammers. If you have crypto holdings,
why are you taking that financial risk to support a crime ecosystem?
TL;DR: Crypto-currencies: not money; not secure; not stable; most crypto-coins go to zero value; enables, legitimizes and funds criminal activity; blockchain is not really anonymous; makes your electrical bill higher; makes the Internet a more expensive and dangerous place for regular users.
Funny thought. Some crypto-fans think crypto-currency is a way to hide their assets and dealings from the 'government'. And the fraudsters LOVE that you're trying to hide your financial activity from the 'government', because that means you are less likely to call the cops when the bad guys burn you. But it turns out there's another currency that can also evade a digital trail: cash. You know - actual legal tender you can use to pay for things. No transaction fees. No need to convert from crypto to real money via a questionable on-line 'exchange' to actually spend it. Doesn't disappear from bank accounts due to fraud or vary in value due to speculation compared to actual money, because it IS actual money.
Cash has some other advantages, like it works when your credit/debit card stops working (been there), or the point
of sale terminal goes down (been there, too) or the network blinks out locking up the ATM, possibly with your card
in it (yep, and bank staff can't retrieve it for you, only ATM staff can - and novice staff can't do anything for
you - like verify you exist - if the network is down). And definitely, a hostile power or ransomware profiteers
would NEVER target a bank or financial data network because they would not want to inconvenience you.
(I especially like my local bank's new policy of denying physical access to their ATMs outside business hours.)
Turns out I'm not the only one that sees some value in keeping some cash in hand, or at least out of the bank's
hands for doing the occasional transaction.
https://www.dailymail.co.uk/news/article-14527137/Barefoot-Investor-Scott-Pape-cashless-society.html
Pro Tip: NEVER tell a restaurant you intend to pay in cash until the bill is presented. If the power goes
out during your meal and they lose your order history or simply can't process your payment electronically
- now the expectation - you might be able to gain a free meal out of their problem. Major storms can
contribute (also been there, and have most likely done enough business there since over the years that
they could afford that loss.
P.S. Restaurant owners: it might be worth having a UPS on-site to keep
your computer systems alive during an outage if you're that dependent on it. If you can't print a
receipt, you can't bill the customer.
Sounds about right for a crypto-currency fan. Steal the electricity, and you can make money at crypto-mining.
Sounds like the crypto market business model in microcosm.
Cryptominers made $100,000 from mining at an Airbnb for three weeks - the guests ran up a $1,500 electricity bill (Tom's Hardware 2024.08.15)
I doubt they made that much, or they could afford their own electricity bill.
Crypto firm diverted $13M in assets, securities commission finds (CBC 2024.08.12)
"Mixer" Bitcoin Fog Operator Sentenced for Money Laundering Conspiracy (U.S. DoJ Archives 2024.11.08)
But the point of the operation was money laundering via 'fogging' Bitcoin and altcoins, and money laundering is a crime.
Another threat to the value of crypto-currency: quantum computing
So the intrinsic value of crypto-currency is zero, possibly actually negative (transaction fees, exchange computers,
computers holding copies of the blockchains).
It's fully based on the
cost of burning electricity to generate nothing but blockchain ledger entries. You can't turn a crypto-currency
unit back into electricity, or anything else with intrinsic value (e.g. food, metals, heating fuel ...) Only
exchange it for real currency (typically sovereign fiat currency), in order to extract any real value from it.
So, in simple terms, owning crypto-currency is the equivalent of getting a certificate for burning a real asset,
and continues to hold value because people continue gambling computer hardware and electricity to create more
such units (which is kind of a Ponzi scheme at heart). But so long as it takes real resources, time and some
effort to make additional units, existing units have some claim to equivalent unit value.
But, what happens if somebody can start generating new units essentially instantly and at near-zero cost?
That's the actual promise of quantum computing in terms of solving the creation of crypto units. Yes, the
entry cost of getting to this threshold is high (so far), but it seems inevitable someone (country, corporation or
criminal organization) will get there before long. Within minutes, they will have a virtual monopoly on
whichever crypto-currencies they target. Eventually, that will be all of them. At that point, they alone
will determine the value of crypto-currencies and your investment in them. When the second player with that
capacity arrives on the scene, they will compete for selling future crypto units, and unless they collaborate,
the competition will inevitably mean the the value of new crypto units will dive to near zero.
TL;DR: quantum computing means crypto currencies will all go to zero value, wiping out investors'
cryto-gamblers holdings.
Chinese researchers break RSA encryption with a quantum computer
RSA is encryption. Crypto-currency is encryption. These researchers broke RSA encryption. What comes next?
Breaking crypto-currency encryption.
US achieves superconductor breakthrough, can benefit quantum computing (Interesting Engineering 2024.08.25)
Is this the end of Bitcoin? Google unveils quantum chip 'Willow' — Is Bitcoin's security at risk? (AMB Crypto 2024.12.10)
The bitcoin ATM has emerged as one of cryptocurrency's biggest threats (CNBC 2024.09.08)
Imagine that, the criminals have found another way to rip off people gullible enough to hold crypto-currency.
"In the U.S, losses from scams via crypto ATMs exceeded $120 million in 2023."
The FBI secretly created a coin to investigate crypto pump-and-dump schemes (The Verge 2024.10.10)
"What the FBI uncovered in this case is essentially a new twist to old-school financial crime," Jodi Cohen,
the special agent in charge of the FBI’s Boston division, said in a statement. "What we uncovered has resulted
in charges against the leadership of four cryptocurrency companies, and four crypto 'market makers' and their
employees who are accused of spearheading a sophisticated trading scheme that allegedly bilked honest investors
out of millions of dollars."
Crypto: designed to shelter criminal financial transactions; now used to bilk honest investors. Win-win for the bad guys.
Deepfakes Can Fool Facial Recognition on Crypto Exchanges (Tech Republic 2024.10.11)
Here we have an AI-crypto crime cross-over. Perhaps you should not put up really good images of yourself on Facecrook,
and definitely not tag them with your name. However, you can't control what your 'friends' do.
Bitcoin Is Going to Be the Nail in Our Climate Coffin
As I have written elsewhere, crypto-currency units are just receipts for wasted electricity. Basically, it has about the
same intrinsic value as the receipt for the non-tax-deductible meal you bought for your family. A scrap of possibly recyclable paper.
Unsurprisingly, wasting electricity isn't good for the environment, or the long-term survival of our species on this planet.
One possible mitigaton measure: require all declared crypto-miners to demonstrate they have installed enough green energy
capacity to at least power their crypto-mining operations, be it wind-power, micro-hydro, solar or whatever, or shut them down.
Upsides, the miners can keep operating when there is a grid outage. Crypto-miners won't be a burden on existing grid users and power
generators, which are often subsidized by taxpayers. Crypto-miner purchases of renewable energy equipment will help lower costs via economies of scale for future buyers,
and presumably their future expansions. We'll know that crypto-miners aren't stealing power from others.
And when their ventures fail, that additional non-polluting generation capacity
can be picked up at the auctions to improve overall sustainability of electricity generation.
The $51 Billion Crypto Crime Industry Is Adopting Stablecoins (Forbes 2025.01.19)
Crypto-currency crime is so big now it has gone corporate and had to expand into stablecoins - not enough crime channels left.
Trump finds a new way for foreign governments to pay him off: Crypto (Washington Post 2025.01.21)
More crime enabled by cryptocurrency. Also $BARRON was a scam to fleece the gullible.
Hackers steal $1.5bn from crypto exchange in 'biggest digital heist ever' (The Guardian 2025.02.23)
Of course your money is safe in an unregulated, for-profit crypto-currency 'exchange' that skimps on security. Except not.
Thank you for making crypto-crime lucrative and enriching Kim Jong Un, and yes, you will pay for it somehow even if ByBit survives.
North Korean hackers ‘took just two minutes’ to pull off record $1.5bn heist (The Telegraph 2025.02.28)
Not the first time ByBit has been a bad news headline, but people still leave their 'money' there. Sigh.
SEC files criminal complaint against three offenders related to the Website: Bybit.com for operating digital asset exchange business without license
Bitcoin Reserve Bills Are Failing in Quick Succession in States (Bloomberg 2025.02.28)
If U.S. states don't trust crypto-currency as a reserve asset, why would you?
Why is Crypto Going Down And When Will Crypto Go Back up? (99Bitcoins 2025.02.28)
What crypt-oh "needs is trust". Question: why would anyone "trust" a pseudo-asset that represents wasted electricity,
has no intrinsic value, was designed to enable crime, and is largely managed by criminals? Why assume it's going back up?
Sudden $1 Trillion Crypto Market Shock Sees Bitcoin Plunge Under $80,000 Price (Forbes 2025.02.28)
Is this a good time to recall Poilievre's plan to run Canada using Bitcoin to replace the Canadian dollar,
so government payments like pensions would depend on crypto-currency prices?
Bitcoin isn't a worthy reserve asset, Swiss National Bank president says: Report (TradingView 2025.03.01)
Bing, Bing, Bing - we have a winner! More correct: Bitcoin isn't an asset at all; it's a tool for criminals.
Call-centre crypto scammers unmasked as data leak exposes their schemes (CBC 2025.03.05)
Files reveal every step of the ruse, from phony articles on X to counterfeit IDs and fake saviours (and while you're thinking about it, get off X(odus)
Cryptocurrency's transparency is a mirage: New research shows a small group of insiders influence its value (The Conversation 2025.03.1)
Designed to be valued based on hype (bubbles), and not on any intrinsic asset value.
"Not only are memecoins risky, but they come with a significant risk of insider trading." If you aren't an insider, you can't win.
Crypto Password-Cracking Firm Unciphered in Turmoil Over Co-Founder's Controversial Past (CBC 2025.03.14)
It's as if crypto-currency just attracts criminals. Oh, wait, it was designed for criminals.
Malware in Cracked TradingView App Has Been Draining Crypto Wallets (decrypt 2025.03.20)
"Blockchain analytics firm Chainalysis estimates there was $51 billion in illicit transaction volume in the past year."
Don't Put Your Banking or Other Financial Information on Your Android or IOS device
From the outset, the mobile devices were about convenience, getting fast to market, getting sticker price down, and never security.
Now, those vendors are trying to bolt on security features and layers, but they're predestined to fail
because security was never part of the core product (hardware, OS or bundled software).
Yes, I still miss Blackberrys; at least RIM / BB could spell security.
As the economy tanks and people become less financially secure, the scamsters and thieves are getting more
greedy and sophisticated - far more capable than regular folks who just use their smartphones and tablets
to get through the day. Banks have pretty good cybersecurity staff. Banks don't put their data on smartphones
or tablets.
If you are going to put your banking information on your devices or in an 'app', make sure you
keep it secure. The digital ecosystem is not designed to do that for you, it's designed to make your
devices more vulnerable.
Data-stealing malware infections increased sevenfold since 2020, Kaspersky experts say
New 'Brokewell' Android malware can steal user data and access banking apps
And we have mounting evidence that when your device is compromised, the banks will not help you,
but will instead blame you for allowing your device to be infected and give the bad guys the
access to take your money. Banks' cyber-security staff are employed to keep the bank's money
safe, not your money.
Cybercriminals Deploy New Malware to Steal Data via Android's Near Field Communication (NFC) (CoinTelegraph 2024.08.16)
For mortals, that's 'tap' technology.
Speaking of tap technology, turns out RFID cards also have security issues, at the hardware level.
RFID cards could turn into a global security mess after discovery of hardware backdoor (TechSpot 2024.08.26)/P>
Octo2 banking trojan is taking over Android phones and stealing cash — how to stay safe (Tom's Guide 2024.09.24)
Short form, don't put your banking or other confidential credentials on your Android device.
Four clues your phone is SPYING on you and even listening through microphone – don't let hackers drain your bank (The U.S. Sun 2025.02.27)
TL;DR: Don't bank on your phone. It's designed to be insecure.
Even your bank card could be vulnerable to cracking to empty your accounts
Android malware steals payment card data using previously unseen technique (Ars Technica 2024.08.23)
As I have said before, banks and their cybersecurity people and systems are there to protect the bank,
not customers.
RBC customers outraged over partial refund after unauthorized withdrawals (Global News 2024.09.09)
If you aren't happy with a bank, move to another institution. Credit unions have a reputation for caring about members (customers).
1.7 million people hit in massive credit card data breach — what to do now Tom's Guide 2024.09.09
Names, addresses, card numbers and other sensitive data exposed
Android malware "FakeCall" now reroutes bank calls to attackers Bleeping Computer 2024.10.30
Don't call your bank from your Android phone. Vendors of personal electronic devices have to start taking personal information
and general operating security seriously. So far, they don't, so you're on your own. The bad guys are well funded.
Telephone Scams
If you don't recognize the incoming number, why are you answering the phone? Due to phone number (Caller ID) spoofing and the proliferation of telephone scam criminals, your phone is not safe. It boggles me that governments, law enforcement agencies and telcos are not actively combatting this activity. The telcos should value the montly revenue from legitimate customers over the revenue they get from the criminals. They should be aware of the 'DO-NOT-CALL' registries for telemarketers and have a pretty good idea from calling volume and patterns as to who are telemarketers. Just as they can display Caller-ID, the telcos could also display a warning symbol of possible scammer making the call.
For security, stop picking up the phone TechCrunch (2024.09.07)
By the way, the Canada Revenue Agency, a bank or a credit card company will NEVER (repeat NEVER) ask you to pay for anything using gift cards or BitCoin. In case I wasn't clear: NEVER!!
Gone Phishing
The front-door for malware and cyber-criminals into your computer / tablet / smartphone and EVERYTHING your devices know about (e.g. your banking information) is clicking on links in your email and social media feeds.
90% of Data Breaches are From Phishing
If you think you're being careful, ask yourself, are you paranoid enough to beat the bad guys EVERY time?
Forget phishing, now "mishing" is the new security threat to worry about
Malware
YAAM - Yet Another Android Malware
Android banking Trojan evolves to evade detection and strike globally
The convenience of using your smartphone to manage your finances and pretend to be a tap credit or
debit card seems to have a lot of appeal. Just remember what you are putting at risk if you do that.
You don't know what permissions an app will really take when you load it, and updates for previously
safe apps can bring malware to your device. I miss BlackBerry Shield for Android, which actually analyzed apps
before you installed them and told you what permissions they were taking.
Banks have big teams of cybersecurity experts looking for such issues. Two things about that.
a) they're playing defence, and they don't have a perfect record on detecting and defending, and,
b) their job is to protect the bank, not you.
New Android Warning As Hackers Install Backdoor On 1.3 Million TV Boxes (Forbes 2024.09.13)
Android is free software from the very-much-for-profit Google enterprise. It is not intended to provide you
with a secure operating system. It is intended to harvest your personal online behaviour information and sell
it to advertisers and others interested in 'data analytics' based on your personal information.
Skill-testing question for today? When is the last time you updated the operating system on your TV set-top box?
(Do you even know how that is done?)
5,000 CAPTCHA Tests Used As Infostealer Gateways—Do Not Complete Them (Forbes 2025.03.01)
If you surf onto a site and it asks you to complete a Captcha 'challenge', even just clicking on the "I'm not a robot" checkmark,
DO NOT complete it. Just back out of the site.
Hackers hijack over 16,000 TP-Link network devices, creating a big ol' botnet that's absolutely slamming Microsoft Azure accounts
When was the last time you turned it off and on again? In this case, it's probably enough to shut down the attack vector.
However, in general, the 'set-and-forget' devices on the IoT are designed to be cheap, moderately reliable, but security is low on
the design requirements list. At a minimum, please reset the password from the factory default to something else to at least
slow down the badbots.
Ransomware and Buying Your Data / System Access Back
Of course you can trust the criminals that trespassed onto your computer and data in order to steal from you.
Clearly these are trustworthy, honourable people who would not lie to you or cheat you. Only, NOT! That's why
you're in this mess in the first place.
So you paid a ransom demand … and now the decryptor doesn't work The Register (2024.09.11)
But suppose you pay the ransom and the lock-out decryption does work.
Happy day for the criminals because: a) they know you'll pay to get your access back; and b) they
already know how to compromise your system, so they can just do it again UNLESS the first thing you do
is figure out how they attacked you the first time and fix that problem permanently. You probably need
external help with that, because if you let the vulnerability happen in the first place, you probably
aren't the one to figure it out, and the bad guys could have inserted new back-door access points as part
of cracking your system.
Turns out businesses aren't very good at protecting your personal data against breaches
Canadian companies struggle to defend against data breaches as incidents mount
Which means you need to be even better at protecting your personal information than they are.
(P.S. Econogics does not store any customer information in an on-line database. We're paranoid on your behalf.)
Calling it Agile Did Not Make it So
What is this strange feeling? Is it vindication? After a couple of decades of ranting about 'Agile' and
another rote system of building software applications (which we used to call 'waterfall'), it seems that real system
designers have finally realized that the Agile emperor has no clothes.
[dead link: https://medium.com/developer-rants/agile-has-failed-officially-8136b0522c49] Agile has failed. Officially.
But not to worry, it's just in time for the snake-oil sales folks to claim AI will do all the systems design and development we will need. Just don't worry about that fact that you don't know what your application is actually doing, or how to fix it when it goes wrong. Eventually, this will lead to something like a 'right-to-repair' movement for software.
Or we could try something really novel; using real human intelligence to understand the problems, figure out how to fix them in a consistent, rational (not capitalized) structure, build with tools that can be fixed when issues arise, and hang onto skilled practitioners because they are valued and needed because things change, and systems have to adapt. Worked for me.
In days where we bemoan lost productivity and desperately seek 'competitive advantage', it is ironic that our C-suites have gone all-in on using me-too ERP systems which are frightening inflexible and increasingly developed outside our borders in countries that are not considered overly friendly. E.g., if the government of India can sanction the murder of Canadian citizens in Canada, why would they hesitate to cripple software used by Canadian companies?
Data Breaches (your personal information)
TL;DR If your personal data is on a device which is connected to the Internet, it is NOT safe.
Take whatever precautions you can, and use available safeguards.
The Slow-Burn Nightmare of the National Public Data Breach (Wired 2024.08.16)
March 2024: I'm tired of trying to save people from crackers, blackhats, malware, ransomware and other cyber vandals and perpetrators. Fortunately, my tax dollars now apparently support the information you should need for safe-surfing at Get Cybersafe https://www.getcybersafe.gc.ca/en (at least until the GoC shuffles all their websites again). (Dead links are the constant bane of my trying to provide connections to useful online information.)The rest of this page is provided for historical reference.
Last updated 2009.11.23
The World Wide Web, cyberspace and personal computing in general are wonderful things, but they are also big and nebulous and carry some risks. It pays to take some precautions to protect your time and your information investments. We have worked intensively with computers for over twenty years, from microcomputers to mainframes. We have learned a few things along the way, which can be of benefit to you.
Startup Media | Backups | Housekeeping | Viruses | Hoaxes | Netiquette | Broken Links | Web Ads
Startup/Recovery Media
Go find your startup diskette (or CD-ROM or Zip disk or whatever media it is on). Now!
Got it? Good. Make a point of starting your system from this media in the next while. Make sure it behaves as expected. If not, make or get a new one, and test the new one. Once you have a known good startup media, put it away again in a safe, easily accessible place. Test it occasionally.
Couldn't find it or don't have one? Go, make one as soon as you possibly can and test it to ensure it works correctly. In the event of a system failure or a severe virus attack, this may be your lifeline to recovering your computer and your data.
Backups
Thou shalt make copies of valued data.
Inserting a 2025 story to add a laptop / mobile device risk flavour
His laptop with 4 years of cancer research was stolen. Now he wants the city to take theft more seriously
London, Ontario 2025.06.02 (CBC)
You can read the news story here:
https://www.cbc.ca/news/canada/london/his-laptop-with-4-years-of-cancer-research-was-stolen-now-he-wants-the-city-to-take-theft-more-seriously-1.7550223
The laptop was stolen from a car parked outside a south London bowling alley in April
Two external hard drives with the laptop were also stolen. Those external drives were the only backups.
If the data is valuable to you, make the backups, AND keep a copy in a safe place separately from the primary computer.
If you are one of the few that actually make regular backups of your computer system, and test them, no need to spend your time reading the rest of this section. Unfortunately, those that need to read this the most will probably not do so.
Hardware fails. Viruses attack. Power fluctuates or fails. Files are deleted unintentionally, and occasionally, deliberately. Upgrades have unintended consequences. Those files you knew you would never need again, well, surprise, now you need them again. Spilled coffee does not enhance system performance. Whatever the cause, it is not a matter of "IF", it is a matter of "WHEN". Eventually, you will need to retrieve a file that is no longer on your system. And after many years of experience, the only reliable means I have found to accomplish a resurrection from the electronic hereafter is a backup. Simply put, it is a copy of the files on your system as of a specific point in time.
Computers have an annoying tendency to fail when you can least afford it. However, they will fail. Most people learn this the hard way, just after they really needed to know. Occasionally you will get lucky. Perhaps there is a fix for the virus that attacked your system that will repair most or even all of the damage, and you will know enough to be find it and administer it in time. Perhaps someone you know has a copy of the file you need and can provide it to you in a timely manner. Perhaps you have an IT support group at your disposal with enough resources to respond to your crisis right when you need them, even at 2:00 a.m. on Saturday morning as you are working the weekend to meet a Monday morning submission deadline. Perhaps you have friends that just love to drop the rest of their life to come and rescue you from your "File not found" error. (If you have just found yourself in one of these situations, I am not your friend.) If you are the beneficiary of such good fortune, good for you. However, in my experience, depending on good luck is a poor long-term strategy.
There are those that believe in mirrored and RAID disk drive
systems to protect their data. I have used both and think highly
of them. But they are not backups. They simply provide some
redundancy to protect you from a minor hardware failure. They
cannot help you to retrieve a file that was intentionally deleted
a couple of weeks ago, or damaged by a virus or lost in fire or
flood. I have worked for many years as a computer systems
professional, and I can assure you that every large system I ever
worked on, including those with mirrored drives and RAID arrays,
had a regular schedule of independent backups to a separate media,
and those media were taken off-site for safe storage. It isn't
just a matter of habit, it's simply good business. In any system I
have ever worked with, the data stored on the system is far more
valuable than the hardware, software or facilities housing them.
If the computer room burns up, that is a major headache, and it
will typically take days to get an equivalent facility back into
operation. However, if you lose the company's data (customer
contacts, customer history, inventory records, employee records,
accounts receivable, accounts payable, taxes collected and
remitted), well, then you're out of business. Count on it. You may
think you can recover, but the first irate customer or lawyer that
finds out your data is toast will finish you off. Guaranteed. And
that applies to a one-person operation using a single small
computer (even as small as a Blackberry or a Palm Pilot or other
PDA or a laptop) just as surely as a Fortune 500 company with
multiple mainframes. Don't just take my word for it.
[Link has bitrotted: http://www.soho.org/Technology_Articles/data_disaster.htm] SOHO
on Data Disaster!! Consequences And Avoidance
[Link has bitrotted: http://www.bizjournals.com/extraedge/consultants/savvy_business_shopper/2002/09/09/column304.html]
BizJournals.com on Backups
and there are lots of companies selling various
products to help you protect your data with their own messages.
(Which should tell you that there are not any one-size-fits-all
solutions.)
The need for backups applies to personal computers as well as business machines. Perhaps your livelihood is not at stake, but consider how much effort it would take to recover the information on your computer if it were unexpectedly wiped clean. Are you prepared to pay a couple of hundred dollars to avoid that effort? If so, then you should be doing backups on your system. By way of illustration, we are familiar with the case of a gentleman that was doing research for a book using a personal computer. He had collected a couple of years worth of research notes, including interviews and transcriptions from rare documents while travelling. He had written about half the book as well. Then his hard drive failed. No backups - never saw the need. A disaster recovery firm attempted to recover some data from the hard drive, but with little success for significant expense. He recovered some material from handwritten notes, memory and renewed correspondence, but most of the material was gone forever. And no book was produced. It's your computer and your information, so it's your decision. Take the risk, or take precautions?
Backups are not an expense. They are insurance. They need to be done regularly and consistently, just like paying premiums. You cannot recover what you have not backed up.
If you are a business in the Ottawa area, and you're currently playing computer roulette with your electronic data (not doing regular backups), please see a computer dealer or service centre about how to backup your system(s), or contact us so we can help you to protect your business. We'd rather see you as a client than as another bankruptcy statistic. If you have a personal or home-based system in the Ottawa area with more data to be backed up than fits comfortably onto a few diskettes, we are prepared to assist you as well. E-mail us with your contact information, and we will discuss how to protect your data. In general, we will recommend a backup strategy and installation of hardware and media that your or your staff will use that are appropriate to your needs. If appropriate, we can also provide a mobile backup service at your site on a scheduled basis, but this is usually not as cost-effective.
Once you have established a reliable means of backing up your files, test the backup on occasion. A backup you can't read is worse than useless. A quick and simple test involves renaming a file that resides on your hard drive, then restoring the file from the backup. Then compare the two versions of the file, either manually or using a utility program for this purpose (if your system has one). If the restore succeeds, you can delete the renamed version. If the restore fails, you can always rename the test file back to its original name. Then, find out why, and correct the problem, then do your backup again, and test it again (until it works).
There are several kinds of backup devices and procedures. Do yourself a favour, and get a backup facility that allows you to recover individual files, groups of files by directory name or wildcard, or the entire system. We also recommend the use of full backups where time and backup media make this practical, and keeping at least three generations of backups on various media. Finally, if it is convenient, keep your most recent backup in a place remote from your computer (preferably a different building) but accessible if you need to get it in a hurry. For a small business, this may be at the owner's or an employee's home. For a major business, another location in the same city may be appropriate, or there are companies that provide this service with periodic pick-up and drop-off services. For home users, perhaps the home of a relative or friend would work. Consider the potential of doing this on a reciprocal basis - you keep one of their backups on your premises, and they keep one of yours on theirs. Of course, don't do this with anyone who you don't want having access to your information.
Backups. Don't compute without them!
Housekeeping
Computers work based on logic. They work better if you use them logically. That applies to how you organize your files. Most operating systems support folders or directories. This is simply a way to divide up your files into logical (to you) groups. For most people, it makes sense to keep their personal letters (e-mails) separately from their financial records. It also makes sense to keep program files (that will probably not change much over time) from data files (that may appear, disappear and be modified frequently). If you have files that pertain to chronological periods, it may make sense to organize them into folders by time periods, say a main folder for each year and sub-folders for each month (and sub-sub-folders for weeks or days if appropriate).
Give your files names that are meaningful to you. It is frustrating and time consuming to spend time looking for a file you know is on your computer, but you can't find because it was named "xz7ty4wv" and is lost amongst other files named in alphabet-soup mode.
Disk space is relatively cheap today compared to the past, so there is a tendency to keep files forever. However, the cost associated with this practice is not the additional disks, it is the time spent doing backups of that data and the time spent wading through endless lists of files when your want to open an existing file. Also, while you are required to keep up to seven years of financial records for tax purposes in many jurisdictions, if you keep more, they can also be used by tax auditors. Even if you have absolutely nothing to hide, why invite them to stay longer by giving them more to look at?
Viruses
I am using the term "virus" here to cover a whole range of nasties which may be more properly called worms, trojans, viruses, etc.
If you have ever been up all night with a sick computer, you know the novelty wears off fast. You're tired, you're desperate, you're frustrated and angry, and clutching at straws, and that last time you just hit Enter or clicked on the mouse just did even more damage. Save yourself from this fate. Go and buy a known anti-virus package from a reputable computer dealer, in a sealed package. Then install it, and keep it up to date. Then, use your computer as if you did not have an anti-virus package on it. Remain vigilant. There are viruses that target anti-virus software first, so that the defence is rendered blind to the invader. Periodically, surf to the website for the vendor for your anti-virus product. If you cannot reach it, that could be a symptom of a virus attack.
We do not sell anti-virus software, or hold stock in companies that sell anti-virus software, or recommend one package over another. So, please believe that this plea is for your protection from software viruses, and not for our benefit. (Actually, we might be financially better off if people needed to hire us to try to salvage their computers after virus damage, but we'd prefer you not have to make that call.)
However, even having current anti-virus protection and practicing safe computing may not provide you with 100% protection, so you should still do your backups. The sad fact is that there are malicious people out there continuing to develop new types of destructive "bugs" and variants on existing ones to wreak havoc with your computer, your data and your life. And they are always searching for new ways to infiltrate your computer. They can arrive via e-mail attachments, in pirated software, in word-processing documents, and very occasionally, even in shrink-wrapped commercial software. Occasionally, the viruses proliferate faster than the anti-virus forces can develop and propagate protection against the bad stuff.
By all means, learn more about these horrible chunks of misbegotten code. The more you know, the better you will be able to protect yourself and slow their spread to others. Here are some sites worth checking (even before you think you have a virus on your system).
For the more technically oriented.
[dead link: http://www.wildlist.org/">The Wildlist.Org Virus Site]
The real damage done by viruses has engendered another annoyance, the virus hoax. The hoax will not damage your system. Instead, it creates a level of anxiety in computer users that serves no purpose, and it clutters up the Internet with useless e-mail messages. So, the next time you get a well-meaning message about another virus that has not made the news yet but is destroying every computer on the planet, instead of forwarding it to everyone you know, please check to see if it is a hoax. If it is, just send an e-mail reply to the person that notified you, calmly explaining that the message is a hoax, and they too can check on such things in the future before forwarding such messages. How can you check? By searching the Interweeb and surfing to one or more of the websites that keep track of such hoaxes.
Netiquette
In the wilds of cyberspace, where many surf behind the supposed veil of anonymity provided by aliases, avatars, remailers, nicknames and handles, civility is often an early victim. It is a sad commentary on us as a species, and provides ample justification for criminal punishment systems in our societies. The catch is, over time, most of our veils are ripped away if someone wants to work hard enough to uncover who is flaming or spamming them. ("Flaming" is the use of abusive or inflammatory language, primarily via e-mail and on discussion lists and forums. "Spamming" is the practice of using Internet tools for inappropriate commercial purposes.) Why take the risk?
Emoticons
Also known as "smilies", these are the cute little
symbols built from standard characters to denote feelings or
emotions like these:
:-) happy / joke / grin / smile
:-(
unhappy
;-) wink
:-o surprised
:-/ . perplexed (there are
many more)
There are times when humour and sarcasm are not
obvious to all reading an e-mail. While they are intended to be
fun, they can backfire if read the wrong way. If you won't avoid
them, some times emoticons can help convey the meaning that might
otherwise be lost. A simple "<grin>" can often
prevent a lot of damage. And note that not all emoticons come
across well in all fonts.
A marvelous innovation, e-mail has allowed business to move faster. Even more than on-line shopping websites, e-mail has been the tool that has allowed business to speed up its operations, both in-house and business-to-business. E-mail is the real underpinning for electronic workflow processing and distance collaboration and has freed business correspondence from the shackles of paper-handling, manual sorting and physical transport to lightspeed.
On the downside, e-mail has also shed the culture, formality and checks and balances of paper mail. As a result, things are said in e-mails that would never have been committed to paper. Part of that is the informality, part of it the psychological sense that e-mail is somehow not as "real" as paper correspondence, and part of that is the speed of e-mail that removes the opportunity for reflection that occurs in the paper world as a letter awaits transport to the mailbox.
In reality, e-mail is just as "real" as paper mail, and worse, the ease of "carbon-copying" an e-mail means that it will reach a wider distribution than its paper equivalent. Every time you write an e-mail, pause and consider the potential consequences of sending it. Assume that it will surface at the worst possible time in the hands of the worst possible person. If you are libeling someone, assume your e-mail will end up in their hands.
When replying to an e-mail, it is often helpful to intersperse your responses into the original text. When you do this, make sure there is a way to distinguish between the original text and your additions. In some packages, this can be done with different fonts or colours. However, the lowest common denominator (and safest) method, is to mark pre-existing text with a prefix character on each line. The ">" (right chevron) character is commonly used for this purpose. Multiple chevrons can be used to denote multiple generations of comments.
If you are replying to a long e-mail, but your response pertains to only a tiny portion of the original, it is good practice to "snip out" those portions of the original e-mail that are not relevant. This saves those reading your e-mail a lot of time.
Another hazard of e-mail is that it is the delivery mechanism of choice for many computer viruses. Several of the more common e-mail client products (that's the part that resides on your personal computer, and probably is "e-mail" to you), have known deficiencies related to security against viruses. Spend a few minutes surfing the web. If you have the choice of which e-mail client to use, look for a lesser known product that will be less attractive to virus-makers, and probably has a better security record. If you cannot choose your e-mail client (corporate decision), then find out what the security weaknesses of your e-mail client product are. Then, find any patches available for it to correct those issues, or learn to work around those security holes.
Finally, remember your last line of defence will usually be a known, good backup. Keep several versions of your backups. Some viruses take their time making their presence known. So if you only have one recent backup available when you find out about a virus on your computer, there is a reasonable chance that virus has also been stored on your backup.
But for the majority of Internet users, the greatest contribution of e-mail has to be that a good joke can now circle the globe in a matter of minutes.
Broken Links
You are happily surfing along the information superhighway, bouncing around from link to link discovering new information and delights, when you hit one of the potholes - a link that does not work. Such an annoyance. However, the reality is that websites disappear, move and get re-organized. If you discover a broken link, and there is a convenient way to contact the Webmaster for the site that has posted the link to the webpage that is now missing, please take a moment and send the e-mail. It is hard to keep up with all the moving webpages. Typically, the information needed by the Webmaster is the address of the page where the problem occurred, and the address of the link that is no longer working. On the other side of the coin, Webmasters, please make it easy for surfers to reach you with this kind of information (ours is at the bottom of the page). Working together, surfers and Webmasters can patch up the potholes, and make surfing better for all of us.
Water Savers | Econogics Blog | Products and Services | Electric Vehicles | Reducing Your Expenses | Personal Energy Plan | The Emperor's New Hydrogen Economy
This website is powered by renewable
energy.
Return to Econogics Home Page
All material on this Web site is copyrighted by Econogics, Inc. (unless otherwise noted).
This Web site created, maintained and sponsored by Econogics, Inc.
Comments to: Webmaster are welcomed.
![[Image: Econogics logo]](../econlogo.gif)